Wow, it has been two years since last post, and this post will not be mind blowing. For the past couple of years I have been busy building an incident response team and SOC so I have not had a lot of time write much worth posting. I finally got some free time this last week and created a quick and dirty script to create OpenIOC format IOCs from unstructured data. This was a pain point in my teams day to day operations since we use OpenIOC format IOCs for just about every part of our automation to look for known indicators, be in in Splunk or MIR. The script is not complicated but saves a ton of time when you have to import a long list of IOCs (MD5’s, IP’s or domain names). To execute the script all you need is a basic install of python, no other libraries. I’ll walk through an example of its use below. First step is to find a source for IOCs. In a perfect world all IOCs would be in a structured format already but most of the time they are not. In this example I will be creating IOC’s from a a FireEye blog post. If you want to play along here is the site: http://blog.fireeye.com/research/2013/02/operation-beebus.html Just copy the contents the blog post to a file. Once you have the contents copied over execute the script as below, “blobofIOCs” is the copied content:
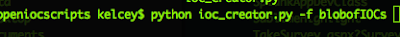
This will create an OpenIOC format IOC in the same directory:
From here you aren’t done it does most of the work but you
have to edit some of the property files and check for BAD IOCs. You can load
the IOC up in Mandiant IOC editor located here:
When parsed it will look similar to the figure below:
“ioc_creator.py” will
generate domain, IP, MD5 hash, registry and file path IOCs. Be sure to change
the name, add groups, and change the description as it defaults to BulkImport .
The IOC will still load into MIR if you don’t change this but you want to
change this data for context if it ever hits. The IOC also has some bad
auto-generated IOCs. The “File Full Path contains “\Windows,” which is a bad
IOC, as well as the single registry path contains. Delete these BAD IOCs out. “ioc_creator.py”
defaults IOC term logic to the following for each IOC term type:
- FileItem/FullPath – contains
- RegistryPath – contains
- Network/DNS – contains
- PortItem/remoteIP – is
- FileItem/Md5sum - is
The auto-generation will catch some very high false positive
IOCs so make sure to use IOC lint and double check what has been auto-generated
for you. In the end my IOC was cleaned
up to look like the following figure:
Please let me know of any bugs or features needed. The
script can be found here:

